Ignorance Is Futile!
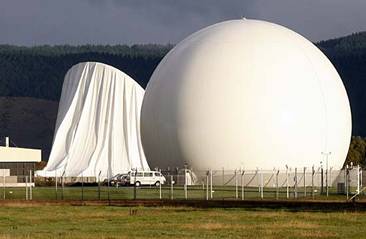
New Zealand's USA spy base, Waihopai, Codename FLINTLOCK -41° 34' 36.00", +173° 44' 20.00"
What can we do to stop the war mongers, the government that -- where it matters (OWNERSHIP+HIERARCHY) -- is 100% controllable by a secret cabal of big corporations?
(see below about the TRACK THE TRACKERS idea!)
Background:
"It (the Waihopai spybase's new dome, being installed today) is inflated totwo PSI (pounds per square inch) above atmospheric pressure and designed toprotect the satellite (sic - dish) from the weather not hide the directionthat the satellite (sic - dish) is pointed, as has been popularly believed".Full story at Fairfax New Zealand Ltd: www.stuff.co.nz/national/2663681/Spy-base-ready-for-new-domeYeah ,right.In which case, why isn't Telecom's big satellite dish at Warkworth under adome to "protect it from the weather"? Or the big satellite dishes on theroofs at TV1 and TV3 in Auckland? Or. Come to think, the hundreds ofthousands of satellite TV dishes on buildings and houses up and down thecountry?Of course the purpose of the domes at Waihopai is to conceal the directionin which the dishes are being pointed, in order to conceal whichinternational civilian telecommunications satellites they are spying on.Actually the Stuff report quoted above has a Freudian slip in that it usesthe word "satellite" instead of "dish". That's it in a nutshell - the domesare to conceal what satellites are being spied on.Please turn the question around and ask the NZ Government CommunicationsSecurity Bureau if they, and their masters in the US National SecurityAgency, don't mind at all if anyone can see which way their spy dishes arepointing and can therefore work out who and what they're spying on? Do aquick Google search of other spybases - Pine Gap in Australia or MenwithHill in the UK, for example - and tell us how many uncovered dishes you cansee as opposed to ones concealed by domes.Please stop falling for the GCSB line that, uniquely, Waihopai's satellitedishes have to be covered by domes to stop them getting wet or blowing away.Murray Horton(03) 3663988/0274 307742
Thank you Murray!
Waihopai is the price that New Zealand pays for being in "the west" i.e. the Anglo American world of murder, blackmail and exploitation?
So, what to do?
Build a laser/radar/ultrasound gizmo that is pointed at the domes,
that (
through the cover)
READS OUT the position that the dome is pointed at,
match it with a satellite database
and publish a daily list (and archive)
of times (and dates) of
what satellite was being listened to.
www.waihopai-watch.org.nz could send out alert emails if there is unusual activity!
It is
the right of you New Zealanders to find out what the spy-agencies are up to.Our whole world is RULED by secret, undemocratic forces! Do NOT allow your government (YOU OWN IT!) to take part in the preparation of wars.
There ARE TOP SECRET bearers. Helen Clarke was one. Why do you think she got a top job at the UN? Because that way she will stay quiet about what she knows about
911 for example. There are many inside jobs (
illusions) created for us. But only
Turkey is draining the swamp and you won't hear about it because the media people rather keep their job. Please take part in networks and JOIN FORCES to make alternative media. It is more important than ever and it will become yet more important if you don't act.
further fun reading for conspiracy deconstruction:
MUST READ:
http://tangibleinfo.blogspot.com/2008/05/learned-helplessness-cia-mind-control.html
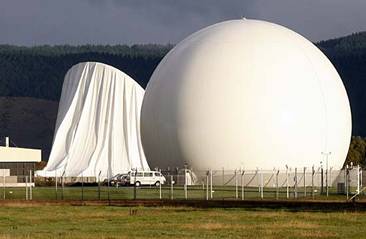
New Zealand's Government Communications Security Bureau operates what it describes as a satellite communications monitoring facility in the Waihopai Valley. First announced in 1987, the facility has been identified by MP Keith Locke as part of ECHELON, the worldwide network of signals interception facilities run by the UKUSA consortium of intelligence agencies (which shares global electronic and signals intelligence among the Intelligence agencies of the US, UK, Canada, Australia and NZ)

It contains two satellite interception dishes (shielded by giant radomes). Few details of the facility are known, but it is believed that it intercepts and processes all phone calls, faxes, e-mail and computer data communications. It is thought that this data is then sorted and shared with the other members of the UKUSA group

The site is a regular target for protesters and activists who are attempting to have the base closed down. The Anti-Bases Campaign have had regular yearly protests at the base.
In 1996 Nicky Hager entered the base at night with John Campbell and a TV3 film crew, and managed to film the operations room through a window.
Hager returned in 1999 with Mikey Havoc and Jeremy Wells (as his "Newsboy" persona). They sneaked into the base and danced in front of cameras for a television show in which Havoc and Newsboy were starring.
In April 2008 Ploughshares Aotearoa or Anzac Ploughshares breached three security fences to enter the base and then used a sickle to deflate the kevlar covering over one of the two satellite dishes. Prime Minister Helen Clark condemned the attack on the spy base as a "senseless act of criminal vandalism"
MUST READ:
http://tangibleinfo.blogspot.com/2008/05/learned-helplessness-cia-mind-control.html What Is Echelon?
Suppose, this past weekend, you sent an email to a friend overseas.
There's a reasonable possibility your communication was intercepted by a global
surveillance system--especially if you happened to discuss last week's bombings
in Iraq.
Or suppose you're stuck in traffic and in your road rage you whip out a
cell phone and angrily call your congressman's office in Washington. There's a
chance the government is listening in on that conversation, too (but only for
the purposes of "training" new eavesdroppers).
Or suppose you're on a foreign trip--vacation, business, relief
work--and you send off a fax to some folks that Washington doesn't view too
keenly. Your message could be taken down and analyzed by the very same system.
That system is called ECHELON and it is controlled by the U.S. National
Security Agency (NSA). In America, it is the Intelligence Network That Dare Not
Be Acknowledged. Questions about it at Defense Department briefings are deftly
deflected. Requests for information about it under the Freedom of Information
Act linger in bureaucratic limbo. Researchers who mention possible uses of it in
the presence of intelligence officials are castigated. Members of
Congress--theoretically, the people's representatives who provide oversight of
the intelligence community--betray no interest in helping anyone find out
anything about it. Media outlets (save the award-winning but low-circulation
Covert Action Quarterly) ignore it. In the official view of the U.S. Government,
it doesn't exist.
But according to current and former intelligence officials, espionage
scholars, Australian and British investigative reporters, and a dogged New
Zealand researcher, it is all too real. Indeed, a soon-to-be finalized European
Parliament report on ECHELON has created quite a stir on the other side of the
Atlantic. The report's revelations are so serious that it strongly recommends an
intensive investigation of NSA operations.
The facts drawn out by these sources reveal ECHELON as a powerful
electronic net--a net that snags from the millions of phone, fax, and modem
signals traversing the globe at any moment selected communications of interest
to a five-nation intelligence alliance. Once intercepted (based on the use of
key words in exchanges), those communiqués are sent in real time to a central
computer system run by the NSA; round-the-clock shifts of American, British,
Australian, Canadian, and New Zealand analysts pour over them in search of . . .
what?
Originally a Cold War tool aimed at the Soviets, ECHELON has been
redirected at civilian targetsworldwide. In fact, as the European Parliament
report noted, political advocacy groups like Amnesty International and
Greenpeace were amongst ECHELON's targets. The system's awesome potential (and
potential for abuse) has spurred some traditional watchdogs to delve deep in
search of its secrets, and even prompted some of its minders within the
intelligence community to come forward. "In some ways," says Reg Whittaker, a
professor and intelligence scholar at Canada's York University, "it's probably
the most useful means of getting at the Cold War intelligence-sharing
relationship that still continues."
While the Central Intelligence Agency--responsible for covert operations
and human-gathered intelligence, or HUMINT--is the spy agency most people think
of, the NSA is, in many respects, the more powerful and important of the U.S.
intelligence organizations. Though its most egregious excesses of 20 years ago
are believed to have been curbed, in addition to monitoring all foreign
communications, it still has the legal authority to intercept any communication
that begins or ends in the U.S., as well as use American citizens' private
communications as fodder for trainee spies. Charged with the gathering of
signals intelligence, or SIGINT--which encompasses all electronic communications
transmissions--the NSA is larger, better funded, and infinitely more secretive
than the CIA. Indeed, the key document that articulates its international role
has never seen the light of day.
That document, known as the UKUSA Agreement, forged an alliance in 1948
among five countries--the U.S., Britain, Australia, Canada, and New Zealand--to
geographically divvy up SIGINT-gathering responsibilities, with the U.S. as
director and main underwriter. Like the NSA--hardly known until the Pike and
Church congressional investigations of the '70s--the other four countries'
SIGINT agencies remain largely unknown and practically free of public oversight.
While other member nations conduct their own operations, there has "never been
any misunderstanding that we're NSA subsidiaries," according to Mike Frost, an
ex-officer in Canada's SIGINT service, the Communications Security Establishment
(CSE). Moreover, all the signatory countries have NSA listening posts within
their borders that operate with little or no input from the local agency.
Like nature, however, journalism abhors a vacuum, and the dearth of
easily accessible data has inspired a cadre of researchers around the world to
monitor the SIGINT community as zealously as possible. It is not, says David
Banisar of the Electronic Privacy Information Center (EPIC), an easy task.
Getting raw data is difficult enough. Figuring out what it means even more so,
he says, thanks in part to the otherwise conservative NSA's very liberal use of
code names--many of which regularly change--for everything from devices to
operations. One that appears to have remained constant, however, is ECHELON.
In 1988, Margaret Newsham, a contract employee from Lockheed posted at
Menwith Hill, the NSA's enormous listening post in Yorkshire, England, filed a
whistleblower suit against Lockheed, charging the company with waste and
mismanagement (the case is currently being appealed after an initial dismissal).
At the same time, Newsham told Congressional investigators that she had
knowledge of illegal eavesdropping on American citizens by NSA personnel. While
a committee began investigating, it never released a report. Nonetheless,
British investigative reporter Duncan Campbell managed to get hold of some of
the committee's findings, including a slew of Menwith Hill operations. Among
them was a project described as the latest installment of a system code named
ECHELON that would enable the five SIGINT agencies "to monitor and analyze
civilian communications into the 21st century."
To SIGINT watchers, the concept wasn't unfamiliar. In the early '80s,
while working on his celebrated study of the NSA, The Puzzle Palace, James
Bamford discovered that the agency was developing a system called PLATFORM,
which would integrate at least 52 separate SIGINT agency computer systems into
one central network run out of Fort Meade, Maryland. Then in 1991, an anonymous
British SIGINT officer told the TV media about an ongoing operation that
intercepted civilian telexes and ran them through computers loaded with a
program called "the Dictionary"--a description that jibed with both Bamford and
Campbell's gleanings.
In 1996, however, intelligence watchdogs and scholars got an avalanche
of answers about ECHELON, upon the publication of Secret Power: New Zealand's
Role in the International Spy Network,written by Nicky Hager. A New Zealand
activist turned investigative author, Hager spent 12 years digging into the ties
between his country's SIGINT agency, the Government Communications Security
Bureau (GCSB), and the NSA. Utilizing leaked material and scores of interviews
with GCSB officers, Hager not only presented a revealing look at the previously
unknown machinations of the GCSB (even New Zealand's Prime Minister was kept in
the dark about its full scope) but also produced a highly detailed description
of ECHELON.
According to Hager's information--which leading SIGINT scholar and
National Security Archive analyst Jeffrey Richelson calls "excellent"--ECHELON
functions as a real-time intercept and processing operation geared toward
civilian communications. Its first component targets international phone company
telecommunications satellites (or Intelsats) from a series of five ground
intercept stations located at Yakima, Washington; Sugar Grove, West Virginia;
Morwenstow in Cornwall, England; Waihopai, New Zealand; and Geraldton,
Australia.
The next component targets other civilian communications satellites,
from a similar array of bases, while the final group of facilities intercept
international communications as they're relayed from undersea cables to
microwave transmitters. According to Hager's sources, each country devises
categories of intercept interest. Then a list of key words or phrases (anything
from personal, business, and organization names to e-mail addresses to phone and
fax numbers) is devised for each category. The categories and keywords are
entered by each country into its "Dictionary" computer, which, after recognizing
keywords, intercepts full transmissions, and sends them to the terminals of
analysts in each of the UKUSA countries.
To the layperson, ECHELON may sound like something out of the X-Files.
But the National Security Archives's Richelson and others maintain that not only
is this not the stuff of science fiction, but is, in some respects, old hat.
More than 20 years ago, then CIA director William Colby matter-of-factly told
congressional investigators that the NSA monitored every overseas call made from
the United States. Two years ago, British Telecom accidentally disclosed in a
court case that it had provided the Menwith Hill station with equipment
potentially allowing it access to hundreds of thousands of European calls a day.
"Let me put it this way," says a former NSA officer. "Consider that anyone can
type a keyword into a Net search engine and get back tens of thousands of hits
in a few seconds." A pause. "Assume that people working on the outer edges have
capabilities far in excess of what you do."
Since earlier this year, ECHELON has caused something of a panic in
Europe, following the disclosure of an official European Parliament report
entitled "In Appraisal of Technologies of Political Control." While the report
did draw needed attention to ECHELON, it--and subsequent European press
coverage--says Richelson, "built ECHELON up into some super-elaborate system
that can listen in on everyone at any time, which goes beyond what Nicky Hager
wrote." Richelson, along with other SIGINT experts, emphasizes that, despite
ECHELON's apparent considerable capabilities, it isn't omniscient.
EPIC's David Banisar points out that despite the high volume of
communications signals relayed by satellite and microwave, a great many
fiber-optic communications--both local and domestic long distance--can't be
intercepted without a direct wiretap. And, adds Canadian ex-spook Mike Frost,
there's a real problem sorting and reading all the data; while ECHELON can
potentially intercept millions of communications, there simply aren't enough
analysts to sort through everything. "Personally, I'm not losing any sleep over
this," says Richelson, "because most of the stuff probably sits stored and
unused at [NSA headquarters in] Fort Meade."
Richelson's position is echoed by some in the intelligence business
("Sure, there's potential for abuse," says one insider, "but who would you
rather have this--us or Saddam Hussein?"). But others don't take such a benign
view. "ECHELON has a huge potential for violating privacy and for abuses of
democracy," says Hager. "Because it's so powerful and its operations are so
secret that there are no real constraints on agencies using it against any
target the government chooses. The excessive secrecy built up in the Cold War
removes any threat of accountability."
The only time the public gets anything resembling oversight, Hager
contends, is when intelligence officials have a crisis of conscience, as several
British spooks did in 1992. In a statement to the London Observer, the spies
said they felt they could "no longer remain silent regarding that which we
regard to be gross malpractice and negligence within the establishment we
operate"--the establishment in question being the Government Communications
Headquarters (GCHQ), Britain's version of the NSA. The operatives said that an
intercept system based on keyword recognition (sound familiar?) was routinely
targeting the communications of Amnesty International and Christian Aid.
Adds Hager, "The use of intelligence services in these cases had nothing
to do with national security, but everything to do with keeping tabs on critics.
The British government frequently finds itself in political conflict with
Amnesty over countries it is supplying arms to or governments with bad human
rights records. ECHELON provides the government with a way to gain advantage
over Amnesty by eavesdropping on their operations."
Hager and others also argue that potential for abuse lies in the
hierarchical and reciprocal nature of the UKUSA alliance. According to data
gathered by congressional committees in the '70s, and accounts of former SIGINT
officers like Frost, UKUSA partners have, from time to time, used each other to
circumvent prohibitions on spying on their own citizens. Frost, for example,
directed Canadian eavesdropping operations against both Americans and
Britons--at the request of both countries' intelligence services, to whom the
surveillance data was subsequently passed.
And British Members of Parliament have raised concerns for years about
the lack of oversight at the NSA's Menwith Hill facility--a base on British soil
with access to British communications yet run by the NSA, which works closely
with the GCHQ. "Given that both the U.S. and Britain turn their electronic
spying systems against many other friendly and allied nations," says Hager, "the
British would be naive not to assume it is happening to them."
David Banisar, the electronic privacy advocate, says that apparently
just asking about ECHELON, or mentioning anything like it, is considered
unreasonable. Since earlier this year, Banisar has been trying to get
information on

ECHELON from the NSA under the Freedom of Information Act.
"They're not exactly forthcoming," he says, explaining that he only recently got
a response in which he was in effect told the European Parliament report "didn't
provide enough information" for the NSA to locate the requested information.
However, Wayne Madsen, co-author with Bamford of the most recent edition of The
Puzzle Palace, was more directly discouraged from investigating ECHELON's
possibly dubious applications, as the following story makes clear. On April 21,
1996, Chechnyen rebel leader Dzokhar Dudayev was killed when a Russian fighter
fired two missiles into his headquarters. At the time of the attack, Dudayev had
been talking on his cellular phone to Russian officials in Moscow about possible
peace negotiations. According to electronics experts, getting a lock on
Dudayev's cell phone signal would not have been difficult, but as Martin
Streetly, editor of Jane's Radar and Electronic Warfare Systems, noted at the
time, the Russian military was so under-equipped and poorly maintained, it was
doubtful a radar intercept plane could have honed in on the signal without help.
Speaking at a conference on Information Warfare a month later, Madsen,
one of the world's leading SIGINT and computer security experts, explained that
it was both politically and technically possible that the NSA helped the
Russians kill Dudayev. Noting the West's interest in preserving the Yeltsin
presidency and in ensuring the safety of an oil consortium's pipeline running
through Chechnya, Madsen explained which NSA satellites could have been used to
intercept Dudayev's call and directionally locate its signal.
This wasn't exactly a stunning revelation: Not only had reports recently
been released in Australia and Switzerland about police tracking suspects by
their cell phone signatures, but Reuters and Agence France-Press had written
about the Dudayev scenario as technically plausible. Still, after his talk,
Madsen was approached by an Air Force officer assigned to the NSA, who tore into
him. "Don't you realize that we have people on the ground over there?" Madsen
recalled the officer seething. "You're talking about things that could put them
in harm's way." Asks Madsen, "If this was how Dudayev died, do you think it's
unreasonable the American people know about the technical aspects behind this
kind of diplomacy?"
Nicky Hager says that the New Zealand intelligence officers who talked
to him did so out of a growing disillusionment with the importance to New
Zealand of access to ECHELON information. In some cases, they said, they had
been so busy listening in on targets of interest to other countries, they
altogether missed opportunities to gather intelligence in New Zealand's national
interest. Ross Coulthart, an investigative reporter with Australia's Nine
Network, says intelligence sources of his have reported similar feelings. "In
the UKUSA intelligence community, there appear, roughly, to be two camps: those
who believe that it's best to fall in line behind the U.S., because the U.S. has
acted as protector and funder and gives us resources and limited participation
in a system we couldn't support ourselves, and those who think the whole thing
is somewhat overrated and sometimes contrary to national interests."
In 1995, for example, Australian intelligence officials leaked a story
to the Australian Broadcasting Company that was, at first blush, damaging to
themselves: Australian intelligence had bugged the Chinese Embassy in Canberra.
However, the Australians had no access to the actual transmissions; they had
merely planted the bugs at the behest of the NSA, which was getting the raw
feed. "Given that both Australian and American companies were bidding for
Chinese wheat contracts at the time," says Coulthart, "it didn't seem like
Australia was getting anything out of this arrangement, so they put the story
out there."
Indeed, says York University's Whittaker, "there's a really important
degree of [economic] tension that wasn't there during the Cold War. On the other
hand, most of the threats perceived as common and borderless--terrorism, nuclear
proliferation, weapons of mass destruction, and global crime--inspire more
cooperation between the UKUSA partners." Hager thinks such cooperation is
certainly merited, but what ECHELON to some extent reflects, he believes, is the
continued erosion of civil liberties and the notion of sovereignty in the name
of security. "Some people I interviewed told me repeatedly, 'It's a good thing
for us to be part of this strong alliance,' " he says. "What it amounts to, in
the end, is an argument for being a cog in a big intelligence machine."
by Jason Vest
Secret Power New Zealand's Role in the International Spy Network by Nicky Hager
Published by Craig Potton Publishing PO Box 555, Nelson, New Zealand First
published 1996 -- Reprinted 1996
It was a grumpy Rob Muldoon who walked across from the Beehive building
to the parliamentary chamber on Tuesday, 12 June 1984. After nine years as an
increasingly embattled prime minister, his rule was disintegrating. That morning
the Leader of the Opposition, David Lange, had announced his party's foreign
policy: New Zealand would be made unconditionally nuclear free and the ANZUS
Treaty would have to be renegotiated. Later that day two National Party MPs
crossed the floor in Parliament to vote for a Labour Party-sponsored Nuclear
Free New Zealand Bill, almost defeating the government. Two days later, blaming
these anti-nuclear defectors, a visibly intoxicated Muldoon threw in the towel
and called an early general election.
That Tuesday afternoon Muldoon was on his way to the 2.30 pm session of
Parliament to read a prepared ministerial statement about a quite different
subject: an obscure agency called the Government Communications Security Bureau
(GCSB). The GCSB had been set up secretly under Muldoon seven years earlier and
had been quietly growing in size throughout his reign.
Until just two months before Muldoon's statement the public had never
even heard of the GCSB. Then peace researcher Owen Wilkes publicised the
existence of a secret radio eavesdropping station run by the GCSB at Tangimoana
Beach, 150 kilometres north of Wellington, revealing for the first time that New
Zealand was involved in this type of intelligence collection. Muldoon was
delivering the government's reply to the publicity.
The brief statement he read was, and remains, the most information the
government has ever been prepared to release about the GCSB and the Tangimoana
station. It acknowledged that the GCSB was involved in signals intelligence "
intercepting the communications of governments, organisations and individuals in
other countries " and said New Zealand had collected that type of intelligence
since the Second World War. It noted that the GCSB liaised closely with
Australia, Canada, the United Kingdom and the United States -- the closest the
government has ever come to talking about the secret five-nation signals
intelligence alliance of which the GCSB is part. But much of the statement was
designed to mislead.
It said that the Tangimoana station did not monitor "New Zealand's
friends in the South Pacific". The big aerials at the station were right then
monitoring nuclear-free Vanuatu, the Solomon Islands, Fiji and all New Zealand's
other South Pacific neighbours -- everyone in the South Pacific, in fact, except
for the Western intelligence allies and their territories. Large quantities of
telexes and Morse code messages sent by long-distance radio in the Pacific
region were being recorded at Tangimoana and sent to the GCSB in Wellington for
distribution to select public servants and to the four intelligence allies.
The statement also said that Tangimoana "does not come under the
direction of any Government, or external agency, other than the New Zealand
Government". In fact, the communications officers in a secure room within the
station were regularly receiving directions from the overseas allies and sending
them back intelligence collected on their behalf.
As soon as Muldoon sat down, the Leader of the Opposition stood up to
respond. Lange, who five weeks later would be Prime Minister, thanked Muldoon
for removing the cause of suspicion which had surrounded the Tangimoana
facility: "In particular, I am grateful that he has given an absolutely
unqualified assurance, which I believe to be of paramount importance, that the
facility is under the full control of the New Zealand Government".
On that same Tuesday one of the GCSB's newest employees left for work
from his home in Khandallah, overlooking Wellington Harbour. He had recently
moved into a key position overseeing the GCSB's policy and planning. After the
GCSB director, this would be the most influential position in determining the
GCSB's direction through its most important period of growth.
Glen Singleton had already made an impression on his colleagues. He was
always polite and sociable, but kept his opinions to himself. Privately, he told
work friends that he did not much like the top people at the GCSB. The other
directors at the GCSB, mostly ex-Air Force, had little in common with his tastes
for antiques, paintings and good food.
Arriving at work, Singleton took the lift to the 14th floor of the
Freyberg Building headquarters. He held his magnetic security pass up to the
right spot on the heavy wooden doors and an unseen black box registered that he
had arrived and automatically opened the door.
In 1984 this top floor contained the GCSB's communications centre, its
24-hour link to its overseas allies, the linguists who translated intercepted
messages and some of the deputy directors. Singleton's office had been
positioned next to the director's, with wide views across the harbour. Staff
recall that "he wandered in and out of the director's office whenever he wanted"
and that he "had the director's ear".
One of the many things Lange did not know about the GCSB when he spoke
in Parliament that afternoon, and would never know, even as Prime Minister, was
that this new officer was not under the control of the New Zealand government at
all. Paid in American dollars and living in a house rented for him by the local
United States embassy, Singleton was an employee of an organisation called the
National Security Agency (NSA).
The NSA is the United States' largest, most secret and probably most
expensive intelligence organisation. It rings the world with intelligence
stations, ships, submarines, aircraft and satellites that act as the "platforms"
for its global electronic spying operations. It has immense intelligence
collecting capabilities. As a remarkable expos, The Puzzle Palace by James
Bamford, shows, the NSA is the big brother of all such intelligence
organisations in the Western world. Its intelligence links with four especially
close allies [Britain, Canada, Australia and New Zealand] are formalised in a
highly secret agreement called UKUSA (pronounced "you-koo-za").
Glen Singleton, still in his early 30s, was on a three-year posting to
the GCSB. He had grown up and been educated in the city of Cleveland in Ohio.
After university study in international relations, he moved to Washington DC to
work for the NSA. In late 1984, after settling in as a foreign officer inside
the GCSB, he was formally appointed as the GCSB's Deputy Director of Policy and
Plans. In this role he advised the GCSB director regularly, directed the work of
other GCSB staff and showed overseas visitors around the GCSB. He visited the
United States embassy often, travelled to the Defence Signals Directorate (DSD)
in Melbourne for meetings and received special private communications from his
Washington bosses. Between 1984 and 1987 he would help to make the plans for a
period of dramatic expansion of the GCSB's operations and capabilities. Later he
would return to the GCSB, having left the NSA, and move into another key role.
Having an American inside the GCSB serving as a foreign liaison officer
would be one thing; allowing an officer from another country to direct policy
and planning seems extraordinary.
During his first three years on the NSA posting Singleton hosted 50 or
more staff from the Wellington intelligence organisations to 4 July parties at
his home. But outside intelligence circles, not even the Prime Minister knew of
his role. As another former Prime Minister said about the GCSB: "You don't know
what you don't know. The whole thing was a bit of an act of faith."
Nineteen eighty-four was a special year for the GCSB. The directors of
the five UKUSA agencies meet together once a year to plan and co-ordinate the
activities of the global intelligence alliance. The agencies take turns to host
the meeting; this year it was the GCSB.
Throughout the early 1980s the GCSB had been expanding: more than
doubling its staff, opening the Tangimoana station and, most pleasing to the
director, establishing various new intelligence analysis sections that had given
the GCSB more to offer within the alliance. Five years before, the organisation
had been squeezed into a corner of Defence headquarters. Now the flags of the
five nations were out on display to greet the UKUSA agency heads to the spacious
new Freyberg Building headquarters. After a special welcome for the overseas
directors, they met in the 14th floor conference room attached to the director's
office, looking out over the pine-clad Wellington hills and, in the foreground,
the Stars and Stripes fluttering outside the nearby American embassy.
The most important visitor was Lieutenant-General Lincoln D. Faurer,
head of the NSA. With him were Peter Marychurch, head of the British Government
Communications Headquarters (GCHQ), Peter Hunt, head of the Canadian
Communications Security Establishment (CSE), and Tim James, head of the
Australian DSD.
Although what was discussed at this meeting is not known, the issues
facing the intelligence alliance were clear. The agenda would have included
plans for new computer and communications systems, which would help to integrate
GCSB operations into the NSA-controlled network, and in particular preparations
for a new, super-secret global intelligence system of which New Zealand would be
an integral part. It would have been made clear that, as part of the new global
system, the NSA required new signals intelligence stations in the South Pacific
by the end of the decade to intercept satellite communications. Over the next
three years, it would be the job of the GCSB Director, Colin Hanson, and his
Australian counterpart to manoeuvre their governments towards approving such a
project.
The meeting may also have discussed the nuclear-free issue, which was
simmering away as Lange's new Labour government settled into office.
Only a few months later, on 27 February 1985, Lange met a United States
State Department official, William Brown, across the dining table of the New
Zealand consul general's residence in Los Angeles. It was a short and tense
meeting.
The nuclear-free issue had come to head in New Zealand. Deciding to
follow public opinion rather than the advice of its officials, the Labour
government had refused entry to the American nuclear-capable warship, USS
Buchanan, and now Lange was being read the list of retaliatory measures that
would be imposed by the United States government. These included cutting many of
the military ties between the two countries; in effect the ANZUS Treaty died
that day. And, as part of the reprisals, according to the then Chief of Defence
Staff, Sir Ewan Jamieson, "the flow of information [from the United States], on
which the New Zealand intelligence community was heavily dependent, was
terminated".
All the journalists, commentators and "well placed sources" were
repeating the same message. As far as the public knew, all intelligence ties
between New Zealand and the United States were severed.
This was completely untrue. While intelligence from military sources was
cut considerably, most of the intelligence flow from the United States continued
uninterrupted. The United States government wanted other countries to see New
Zealand punished for its nuclear-free policies, but the UKUSA alliance was too
valuable to be interrupted by politics.
A few days before Lange's meeting in Los Angeles, the GCSB received a
call from its liaison officer at the NSA's headquarters in Washington DC. Warren
Tucker, who had moved into the position a few weeks before and would later
become Director of Operations back at the GCSB, told the senior GCSB staff that
the announcement was coming but reassured them that his position at the NSA was
secure. While other New Zealand diplomatic staff in Washington were frozen out
by their United States government contacts, Tucker was envied because his
position was largely unaffected.
The communications centre (the "commcen") back in the GCSB's Wellington
headquarters was the first place where practical signs of the Los Angeles
reprisals were noticed. Here mostly ex-Navy communications staff worked around
the clock maintaining contact with the four sister agencies.
Every day, hundreds and hundreds of intelligence reports were spat out
of the large sound-proofed printers, more reports than the small Wellington
intelligence agencies even had time to read. In February 1985, the GCSB was
receiving reports about the minute details of the Iran-Iraq War, Soviets in
Afghanistan, a weekly list of all the Libyan students in Britain and a lot of
other marginally interesting top secret reports. But there was nothing, among
the screeds of reports on international terrorism, about the French DGSE agents
who were right then on their way to New Zealand to become the first foreign
terrorists in New Zealand's history: blowing up the Greenpeace ship Rainbow
Warrior.
Most of the daily flood of overseas reports did not stop. But the
communications staff noticed that the "routing indicators", which show the
origin and destination of documents within the UKUSA system, had been removed
from incoming reports. While the public condemnation of New Zealand's
nuclear-free policy by the United States government increased in pitch, it seems
some strategist in Washington decided there should be no tangible evidence that
United States intelligence reports were still arriving in Wellington. They did
not want to take the risk that one of these documents might one day be held up
in public as evidence that the New Zealand had got away with its nuclear-free
policy.
Later, when the public debate had cooled, the usual routing indicators
quietly reappeared on the overseas reports. While governments, journalists and
the public around the world were led to believe that United States-New Zealand
intelligence ties had been cut, inside the five-agency network it was mostly
business as usual.
The United States military was unsentimental about its decades of
alliance links with the New Zealand armed forces; military exercises, exchanges
and other visible links were completely cut. But New Zealand's involvement in
the UKUSA intelligence alliance, first alluded to in public by Muldoon only nine
months before, was too useful to the overseas allies to be interrupted by a
quarrel over nuclear ships.
Notes Chapter 1
1. The meeting was during the second half of 1984, or possibly the
start of 1985.
2. Ewan Jamieson, Friend or Ally: New Zealand at odds with its past,
Brassey's Australia, Sydney, 1990, p.3.
Ten years later, on Saturday, 15 January 1994, technicians in satellite earth
stations around the Pacific were busy tuning their equipment to a new satellite.
The first of the new generation of Intelsat 7 series satellites, it had been
launched several weeks before, from the European Kourou air base in French
Guyana, and then manoeuvred into position far out in space above the Equator at
174 degrees east, due north of New Zealand above Kiribati.
The 20 Intelsat (International Telecommunications Satellite Organisation)
satellites that ring the world above the Equator carry most of the world's
satellite-relayed international phone calls and messages such as faxes, e-mail
and telexes. The new satellite, Intelsat 701, replaced the 10-year-old Intelsat
510 in the same position. The changeover occurred at 10 pm New Zealand time that
summer evening.
At the GCSB's station at Waihopai, near Blenheim in the north of the South
Island, the radio officer staff were just as busy that evening, setting their
special equipment to intercept the communications which the technicians in
legitimate satellite earth stations would send and receive via the new
satellite. These specially trained radio officers, who learned their skills at
the Tangimoana station, usually work day shifts, but on 15 January 1994 they
worked around the clock, tuning the station's receivers to the frequency bands
the GCSB wanted to intercept, selecting the specific channels within each band
that would yield the types of messages sought within the UKUSA network and then
testing that the high-tech intelligence collection system was working smoothly.
That satellite changeover was a very significant event for the Waihopai station
and the GCSB. Although it would always be only a small component of the global
network, this was the moment when the station came into its own.
There have been various guesses and hints over the years about what the Waihopai
station was set up to monitor -- "sources" in one newspaper said foreign warship
movements; a "senior Telecom executive" told another newspaper it was most
likely "other countries" military communications" -- but, outside a small group
of intelligence staff, no one could do more than theorise. Waihopai was
established specifically to target the international satellite traffic carried
by Intelsat satellites in the Pacific region and its target in the mid-1990s is
the Intelsat 701 that came into service in January 1994, and is the primary
satellite for the Pacific region.
Intelsat satellites carry most of the satellite traffic of interest to
intelligence organisations in the South Pacific: diplomatic communications
between embassies and their home capitals, all manner of government and military
communications, a wide range of business communications, communications of
international organisations and political organisations and the personal
communications of people living throughout the Pacific. The Intelsat 7
satellites can carry an immense number of communications simultaneously. Where
the previous Intelsat 5s could carry 12,000 individual phone or fax circuits at
once, the Intelsat 7s can carry 90,000. All "written" messages are currently
exploited by the GCSB. The other UKUSA agencies monitor phone calls as well.
The key to interception of satellite communications is powerful computers that
search through these masses of messages for ones of interest. The intercept
stations take in millions of messages intended for the legitimate earth stations
served by the satellite and then use computers to search for pre-programmed
addresses and keywords. In this way they select out manageable numbers (hundreds
or thousands) of messages to be searched through and read by intelligence
analysis staff.
Until the Intelsat 701 satellite replaced the older 5 series, all the
communications intercepted at Waihopai could already be got from two existing
UKUSA stations covering the Pacific. But, unlike their predecessors, this new
generation of Intelsat 7s had more precise beams transmitting communications
down to the southern hemisphere. The existing northern hemisphere-based stations
were no longer able to pick up all the southern communications, which is why new
stations were required.
Eleven months later, on 3 December 1994, the other old Intelsat satellite above
the Pacific was replaced by Intelsat 703. Since then Waihopai and its sister
station in Australia constructed at the same time have been the main source of
southern hemisphere Pacific satellite communications for the UKUSA network.
Many people are vaguely aware that a lot of spying occurs, maybe even on them,
but how do we judge if it is ubiquitous or not a worry at all? Is someone
listening every time we pick up the telephone? Are all our Internet or fax
messages being pored over continuously by shadowy figures somewhere in a
windowless building? There is almost never any solid information with which to
judge what is realistic concern and what is silly paranoia.
What follows explains as precisely as possible -- and for the first time in
public -- how the worldwide system works, just how immense and powerful it is
and what it can and cannot do. The electronic spies are not ubiquitous, but the
paranoia is not unfounded.
The global system has a highly secret codename -- ECHELON. It is by far the most
significant system of which the GCSB is a part, and many of the GCSB's daily
operations are based around it. The intelligence agencies will be shocked to see
it named and described for the first time in print. Each station in the ECHELON
network has computers that automatically search through the millions of
intercepted messages for ones containing pre-programmed keywords or fax, telex
and e-mail addresses. For the frequencies and channels selected at a station,
every word of every message is automatically searched (they do not need your
specific telephone number or Internet address on the list).
All the different computers in the network are known, within the UKUSA agencies,
as the ECHELON Dictionaries. Computers that can search for keywords have existed
since at least the 1970s, but the ECHELON system has been designed to
interconnect all these computers and allow the stations to function as
components of an integrated whole. Before this, the UKUSA allies did
intelligence collection operations for each other, but each agency usually
processed and analysed the intercept from its own stations. Mostly, finished
reports rather than raw intercept were exchanged.
Under the ECHELON system, a particular station's Dictionary computer contains
not only its parent agency's chosen keywords, but also a list for each of the
other four agencies. For example, the Waihopai computer has separate search
lists for the NSA, GCHQ, DSD and CSE in addition to its own. So each station
collects all the telephone calls, faxes, telexes, Internet messages and other
electronic communications that its computers have been pre-programmed to select
for all the allies and automatically sends this intelligence to them. This means
that the New Zealand stations are used by the overseas agencies for their
automatic collecting -- while New Zealand does not even know what is being
intercepted from the New Zealand sites for the allies. In return, New Zealand
gets tightly controlled access to a few parts of the system.
When analysts at the agency headquarters in Washington, Ottawa, Cheltenham and
Canberra look through the mass of intercepted satellite communications produced
by this system, it is only in the technical data recorded at the top of each
intercept that they can see whether it was intercepted at Waihopai or at one of
the other stations in the network. Likewise, GCSB staff talk of the other
agencies' stations merely as the various "satellite links" into the integrated
system. The GCSB computers, the stations, the headquarters operations and,
indeed, the GCSB itself function almost entirely as components of this
integrated system.
In addition to satellite communications, the ECHELON system covers a range of
other interception activities, described later. All these operations involve
collection of communications intelligence,<> as opposed to other types of
signals intelligence such as electronic intelligence, which is about the
technical characteristics of other countries' radar and weapon systems.
Interception of international satellite communications began in the early 1970s,
only a few years after the first civilian communications satellites were
launched. At this time the Intelsat satellites, located over the Atlantic,
Pacific and Indian Oceans, simply beamed all their messages down to the entire
hemisphere within their view.
Throughout the 1970s only two stations were required to monitor all the Intelsat
communications in the world: a GCHQ station in the south-west of England had two
dishes, one each for the Atlantic and Indian Ocean Intelsats, and an NSA station
in the western United States had a single dish covering the Pacific Intelsat.
The English station is at Morwenstow, at the edge of high cliffs above the sea
at Sharpnose Point in Cornwall. Opened in 1972-73, shortly after the
introduction of new Intelsat 4 satellites, the Morwenstow station was a joint
British-American venture, set up using United States-supplied computers and
communications equipment, and was located only 110 kilometres from the
legitimate British Telecom satellite station at Goonhilly to the south. In the
1970s the Goonhilly dishes were inclined identically towards the same Atlantic
and Indian Ocean satellites.<>
The Pacific Intelsat satellite was targeted by an NSA station built on a high
basalt tableland inside the 100,000-hectare United States Army Yakima Firing
Centre, in Washington State in the north-west United States, 200 kilometres
south-west of Seattle. Also established in the early 1970s, the Yakima Research
Station initially consisted of a long operations building and the single large
dish. In 1982, a visiting journalist noted that the dish was pointing west, out
above the Pacific to the third of the three Intelsat positions.<>
Yakima is located between the Saddle Mountains and Rattlesnake Hills, in a
desert of canyons, dunes and sheer rock cliffs, where the only vegetation is
grass. The Army leases the land to ranchers who herd their cattle in the shadow
of the dishes. When visited in mid-1995 the Yakima station had five dish
antennae, three facing westwards over the Pacific Ocean and two, including the
original large 1970s dish, facing eastwards. Besides the original operations
building there were several newer buildings, the largest of them two-storey,
concrete and windowless.
Two of the west-facing dishes are targeted on the main Pacific Intelsat
satellites; the Yakima station has been monitoring Pacific Intelsat
communications for the NSA ever since it opened. The orientation of the two
east-facing dishes suggests that they may be targeted on the Atlantic Intelsats,
intercepting communications relayed towards North and South America. One or both
may provide the link between the station and the NSA headquarters in Washington.
The fifth dish at the station is smaller than the rest and faces to the west.
Given its size and orientation, it appears to be the UKUSA site for monitoring
the Inmarsat-2 satellite that provides mobile satellite communications in the
Pacific Ocean area. If so, this is the station that would, for example, have
been monitoring Greenpeace communications during the nuclear testing protests in
the waters around Moruroa Atoll in 1995.
The GCSB has had important links with the Yakima station since 1981, when the
GCSB took over a special, highly secret area of intelligence analysis for the
UKUSA network (see Chapter 6). Telexes intercepted using Yakima's single dish
were first sorted by the Yakima computers, and then subjects allocated to New
Zealand were sent to the GCSB for analysis. The Yakima station had been using
Dictionary-type computers for this searching work for many years before the full
ECHELON system was operating.
Between them, the Morwenstow and Yakima stations covered all Intelsat
interception during the 1970s. But a new generation of Intelsat satellites
launched from the late 1970s required a new configuration of spy stations. The
Intelsat 4A and 5 series satellites differed from earlier ones in that they did
not transmit only to the whole of the side of the world within their view; they
now also had "east and west hemispheric" beams that transmitted separately.<>
For example, Intelsat 510, which operated above the Pacific until its
replacement in December 1994, had one "global" beam covering the whole region,
but all the other transmissions went either to the east or to the west Pacific.
Yakima was not within the "footprint" of any hemispheric beams covering
Australasia, South East Asia and East Asia, making interception of these signals
difficult or impossible.
These changes to Intelsat design meant that the UKUSA alliance required at least
two new stations to maintain its global coverage. Again the GCHQ provided one
and the NSA one. A new NSA station on the east coast of the United States would
cover Atlantic Intelsat traffic beamed down towards North and South America
(Morwenstow covered the eastern Atlantic), and a GCHQ station in Hong Kong would
cover both the western hemisphere of the Pacific Intelsats and the eastern
hemisphere of the Indian Ocean Intelsats.
The site chosen for the new NSA station was hidden in the forested South Fork
Valley in the mountains of West Virginia, about 250 kilometres south-west from
Washington DC, on the edge of the George Washington National Forest, near the
small settlement of Sugar Grove. The site had been used in the 1950s and early
1960s for a failed attempt to spy on Russian radio communications and radars by
means of reflections from the moon. The current satellite interception station
was developed during the late 1970s, when a collection of new satellite dishes
(from 10 to 45 metres in diameter) and the new windowless Raymond E. Linn
Operations Building were constructed. It also incorporated a two-storey
underground operations building already at the site. It started full operations
about 1980.<>
Like Morwenstow and Yakima, Sugar Grove is only 100 kilometres from an
international satellite communications earth station, making it easy to
intercept any "spot" beams directed down to the legitimate stations. In this
case it is the Etam earth station, the main link in the United States with the
Intelsat satellites above the Atlantic Ocean.
The other new station, in Hong Kong, was constructed by the GCHQ also in the
late 1970s. The station, which has since been dismantled, was perched above the
sea on the south side of Hong Kong Island, across Stanley Bay from the British
Stanley Fort military base and right next to high-rise apartments and luxury
housing. In crowded Hong Kong the station's anonymity was assured simply because
there are so many satellite dishes scattered over the island. What helped to
give away this one was the sign, on the entrance to an exclusive housing enclave
across the bay, saying that taking photographs is strictly forbidden. When one
of the Indian guards on the gate was asked why it was forbidden to take photos
of a housing area, he pointed across the bay and said in serious tones,
"Communications facility -- very, very secret".
The Hong Kong station had several satellite dishes and buildings, including a
large windowless concrete building (similar to the ones at Yakima and Sugar
Grove) and a collection of administration and operations buildings running down
the hill into the base from the gates. Intelsat communications intercepted at
the station were seen regularly by GCSB operations staff in Wellington.<>
When visited in August 1994, the station fitted the requirements of the Intelsat
monitoring network. It had one dish pointing up east towards the Pacific
Intelsats, another towards the Indian Ocean Intelsats and a third, for the
station's own communications, pointing up to a United States Defence Satellite
Communications System satellite above the Pacific. Other dishes had perhaps
already been removed. Dismantling of the station began in 1994 -- to ensure it
was removed well before the 1997 changeover to Chinese control of Hong Kong --
and the station's staff left in November that year. News reports said that the
antennae and equipment were being shipped to the DSD-run Shoal Bay station in
Northern Australia, where they would be used for intercepting Chinese
communications.
It is not known how the Hong Kong station has been replaced in the global
network. One of the Australian DSD stations -- either Geraldton or Shoal Bay --
may have taken over some of its work, or it is possible that another north-east
Asian UKUSA station moved into the role. For example, there were developments at
the NSA's Misawa station in northern Japan in the 1980s that would fit well with
the need for expanded Intelsat monitoring.<>
Throughout the 1980s a series of new dishes was also installed at the Morwenstow
station, to keep up with expansion of the Intelsat network. In 1980 it still
required only the two original dishes, but by the early 1990s it had nine
satellite dishes: two inclined towards the two main Indian Ocean Intelsats,
three towards Atlantic Ocean Intelsats, three towards positions above Europe or
the Middle East and one dish covered by a radome.
The Morwenstow, Yakima, Sugar Grove and Hong Kong stations were able to provide
worldwide interception of the international communications carried by Intelsat
throughout the 1980s. The arrangement within the UKUSA alliance was that, while
the NSA and GCHQ ran the four stations, each of the five allies (including the
GCSB) had responsibility for analysing some particular types of the traffic
intercepted at these stations.
Then, in the late 1980s, another phase of development occurred. It may have been
prompted by approaching closure of the Hong Kong station, but a more likely
explanation is that, as we have seen, technological advances in the target
Intelsat satellites again required expansion of the network.
Two UKUSA countries were available to provide southern hemisphere coverage:
Australia and New Zealand. One of the new southern hemisphere stations would be
the GCSB's Waihopai station and the other would be at Geraldton in West
Australia. (Both stations are described in detail later.) The new stations were
operating by 1994 when the new Intelsat 7s began to be introduced. Waihopai had
opened in 1989, with a single dish, initially covering one of the older
generation of Intelsat satellites.
The positioning of the Geraldton station on Australia's extreme west coast was
clearly to allow it to cover the Indian Ocean Intelsats (they all lie within 60
degrees of the station, which allows good reception). Geraldton opened in 1993,
with four dishes, covering the two main Indian Ocean Intelsats (at 60 degrees
and 63 degrees) and possibly a new Asia-Pacific Intelsat introduced in 1992. It
also covers the second of the two Pacific Intelsats, Intelsat 703.
The logic of the system suggests that, at the same time as the Waihopai and
Geraldton stations were added to the network, a seventh, as yet undiscovered,
station may have been installed in the South Atlantic. This station, probably
located on Ascension Island, would complete the 1990s network by intercepting
the Atlantic Intelsats' southern hemisphere communications.<>
New GCSB operations staff attend training sessions that cover the ECHELON
system, showing how the GCSB fits into the system and including maps showing the
network of UKUSA stations around the world. The sessions include briefings on
the Intelsat and the maritime Inmarsat satellites -- their locations, how they
work, what kinds of communications they carry and the technical aspects of their
vulnerability to spying. This is because these are primary targets for the UKUSA
alliance in the Pacific.
But the interception of communications relayed by Intelsat and Inmarsat is only
one component of the global spying network co-ordinated by the ECHELON system.
Other elements include: radio listening posts, including the GCSB's Tangimoana
station; interception stations targeted on other types of communications
satellites; overhead signals intelligence collectors (spy satellites) like those
controlled from the Pine Gap facility in Australia; and secret facilities that
tap directly into land-based telecommunications networks.
What Waihopai, Morwenstow and the other stations do for satellite
communications, another whole network of intercept stations like Tangimoana,
developed since the 1940s, does for radio.
There are several dozen radio interception stations run by the UKUSA allies and
located throughout the world. Many developed in the early years of the Cold War
and, before satellite communications became widespread in the 1980s, were the
main ground signals intelligence stations targeting Soviet communications. Some
stations were also used against regional targets. In the Pacific, for example,
ones with New Zealand staff were used to target groups and governments opposed
by Britain and the United States through a series of conflicts and wars in South
East Asia.
A recent new radio interception station is the Australian DSD station near
Bamaga in northern Queensland, at the tip of Cape York. It was set up in 1988
particularly to monitor radio communications associated with the conflict
between Papua New Guinea and the secessionist movement in Bougainville.<> GCSB
staff are also aware of Australian intercept staff posted in the early 1990s to
the recently opened Tindal Air Force base in northern Australia, suggesting that
an even newer -- as yet undisclosed -- DSD intercept station may have been
established there.
Most of this network of stations target long-range high frequency (HF) radio. A
powerful HF radio transmitter can transmit right around the world, which is why
HF radio has been a major means of international communications and is still
widely used by military forces and by ships and aircraft. Other stations target
short-range communications -- very high frequency and ultra high frequency radio
(VHF and UHF) -- which, among other things, are used extensively for tactical
military communications within a country.
There is a wide variety of these radio interception operations. Some are very
large, with hundreds of staff; others are small -- a few staff hidden inside a
foreign embassy bristling with radio aerials on the roof; others (like the
Bamaga station) are unstaffed, with the signals automatically relayed to other
stations. Because of the peculiarities of radio waves, sometimes stations far
from the target can pick up communications that closer ones cannot.
Each station in this network -- including the GCSB's Tangimoana station -- has a
Dictionary computer like those in the satellite intercept stations. These search
and select from the communications intercepted, in particular radio telexes,
which are still widely used, and make these available to the UKUSA allies
through the ECHELON system.
The UKUSA network of HF stations in the Pacific includes the GCSB's Tangimoana
station (and before it one at Waiouru), five or more DSD stations in Australia,
a CSE station in British Columbia, and NSA stations in Hawaii, Alaska,
California, Japan, Guam, Kwajalein and the Philippines. The NSA is currently
contracting its network of overseas HF stations as part of post-Cold War
rationalisation. This contraction process includes, in Britain, the closure of
the major Chicksands and Edzell stations.
The next component of the ECHELON system covers interception of a range of
satellite communications not carried by Intelsat. In addition to the six or so
UKUSA stations targeting Intelsat satellites, there are another five or more
stations targeting Russian and other regional communications satellites. These
stations are located in Britain, Australia, Canada, Germany and Japan. All of
these stations are part of the ECHELON Dictionary system. It appears that the
GCHQ's Morwenstow station, as well as monitoring Intelsat, also targets some
regional communications satellites.
United States spy satellites, designed to intercept communications from orbit
above the earth, are also likely to be connected into the ECHELON system. These
satellites either move in orbits that criss-cross the earth or, like the
Intelsats, sit above the Equator in geostationary orbit. They have antennae that
can scoop up very large quantities of radio communications from the areas below.
The main ground stations for these satellites, where they feed back the
information they have gathered into the global network, are Pine Gap, run by the
CIA near Alice Springs in central Australia, and the NSA-directed Menwith Hill
and Bad Aibling stations, in England and Germany respectively.<> These
satellites can intercept microwave trunk lines and short-range communications
such as military radios and walkie-talkies. Both of these transmit only line of
sight and so, unlike HF radio, cannot be intercepted from faraway ground
stations.
The final element of the ECHELON system are facilities that tap directly into
land-based telecommunications systems, completing a near total coverage of the
world's communications. Besides satellite and radio, the other main method of
transmitting large quantities of public, business and government communications
is a combination of undersea cables across the oceans and microwave networks
over land. Heavy cables, laid across the seabed between countries, account for a
large proportion of the world's international communications. After they emerge
from the water and join land-based microwave networks, they are very vulnerable
to interception.
The microwave networks are made up of chains of microwave towers relaying
messages from hilltop to hilltop (always in line of sight) across the
countryside. These networks shunt large quantities of communications across a
country. Intercepting them gives access to international undersea communications
(once they surface) and to international communication trunk lines across
continents. They are also an obvious target for large-scale interception of
domestic communications.
Because the facilities required to intercept radio and satellite communications
-- large aerials and dishes -- are difficult to hide for too long, that network
is reasonably well documented. But all that is required to intercept land-based
communication networks is a building situated along the microwave route or a
hidden cable running underground from the legitimate network. For this reason
the worldwide network of facilities to intercept these communications is still
mostly undocumented.
Microwave communications are intercepted in two ways: by ground stations,
located near to and tapping into the microwave routes, and by satellites.
Because of the curvature of the earth, a signals intelligence satellite out in
space can even be directly in the line of a microwave transmission. Although it
sounds technically very difficult, microwave interception from space by United
States spy satellites does occur. <>
A 1994 expos of the Canadian UKUSA agency called Spyworld,<> co-authored by a
previous staff member, Mike Frost, gave the first insights into how much
microwave interception is done. It described UKUSA "embassy collection"
operations, where sophisticated receivers and processors are secretly
transported to their countries' overseas embassies in diplomatic bags and used
to monitor all manner of communications in the foreign capitals.
Since most countries' microwave networks converge on the capital city, embassy
buildings are an ideal site for microwave interception. Protected by diplomatic
privilege, embassies allow the interception to occur from right within the
target country.<> Frost said the operations particularly target microwave
communications, but also other communications including car telephones and
short-range radio transmissions.
According to Frost, Canadian embassy collection began in 1971 following pressure
from the NSA. The NSA provided the equipment (on indefinite loan), trained the
staff, told them what types of transmissions to look for on particular
frequencies and at particular times of day and gave them a search list of NSA
keywords. All the intelligence collected was sent to the NSA for analysis. The
Canadian embassy collection was requested by the NSA to fill gaps in the United
States and British embassy collection operations, which were still occurring in
many capitals around the world when Frost left the CSE in 1990.
Separate sources in Australia have revealed that the DSD also engages in embassy
collection. Leaks in the 1980s described installation of "extraordinarily
sophisticated intercept equipment, known as Reprieve in Australia's High
Commission in Port Moresby, Papua New Guinea and in the embassies in Indonesia
and Thailand. The operations are said to take a whole room of the embassy
buildings and to be able to listen to local telephone calls at will.<> There is
good reason to assume that these operations, too, were prompted by and supported
with equipment and technical advice from the NSA and GCHQ.
Of course, when the microwave route is across one of the UKUSA countries'
territory it is much easier to arrange interception. For example, it is likely
that there is a GCHQ operation intercepting, and feeding through Dictionary
computers, all the trans-Atlantic undersea cable communications that come ashore
in Cornwall.
There are also definitely United States and possibly Canadian facilities for
this type of interception. By far the most important of these is the
NSA-directed Menwith Hill station in Britain. With its 22 satellite terminals
and over 2 hectares of buildings, Menwith Hill is undoubtedly the largest
station in the UKUSA network. In 1992 some 1200 United States personnel were
based there.<> British researcher Duncan Campbell has described how Menwith Hill
taps directly into the British Telecom microwave network, which has actually
been designed with several major microwave links converging on an isolated tower
connected underground into the station.<> The station also intercepts satellite
and radio communications and is a ground station for the electronic
eavesdropping satellites. Each of Menwith Hill's powerful interception and
processing systems presumably has its own Dictionary computers connected into
the ECHELON system.
Menwith Hill, sitting in northern England, several thousand kilometres from the
Persian Gulf, was awarded the NSA's Station of the Year prize for 1991 following
its role in the Gulf War. It is a station which affects people throughout the
world.
In the early 1980s James Bamford uncovered some information about a worldwide
NSA computer system codenamed Platform which, he wrote, "will tie together
fifty-two separate computer systems used throughout the world. Focal point, or
Òhost environmentÓ, for the massive network will be the NSA headquarters at Fort
Meade. Among those included in Platform will be the British SIGINT organisation,
GCHQ. <>
There is little doubt that Platform is the system that links all the major UKUSA
station computers in the ECHELON system. Because it involves
computer-to-computer communications, the GCSB and perhaps DSD were only able to
be integrated into the system in the 1990s when the intelligence and military
organisations in the two countries changed over to new computer-based
communications systems.
The worldwide developments, of which construction of the Waihopai station was
part, were co-ordinated by the NSA as Project P415. Although most of the details
remained hidden, the existence of this highly secret project targeting civilian
communications was publicised in August 1988 in an article by Duncan Campbell.
He described how the UKUSA countries were "soon to embark on a massive,
billion-dollar expansion of their global electronic surveillance system', with
"new stations and monitoring centres ... to be built around the world and a
chain of new satellites launched'.
The satellite interception stations reported to be involved in P415 included the
NSA's Menwith Hill station, the GCHQ's Morwenstow and Hong Kong stations and the
Waihopai and Geraldton stations in the South Pacific. Other countries involved,
presumably via the NSA, were said to be Japan, West Germany and, surprisingly,
the People's Republic of China.
"Both new and existing surveillance systems are highly computerised," Campbell
explained. "They rely on near total interception of international commercial and
satellite communications in order to locate the telephone and other target
messages of target individuals....<>
There were two components to the P415 development, the first being the new
stations required to maintain worldwide interception. More striking, though, was
the expansion of the NSA's ECHELON system, which now links all the Dictionary
computers of all the participating countries.
The ECHELON system has created an awesome spying capacity for the United States,
allowing it to monitor continuously most of the world's communications. It is an
important component of its power and influence in the post-Cold War world order,
and advances in computer processing technology continue to increase this
capacity.
The NSA pushed for the creation of the system and has the supreme position
within it. It has subsidised the allies by providing the sophisticated computer
programmes used in the system, it undertakes the bulk of the interception
operations and, in return, it can be assumed to have full access to all the
allies' capabilities.
Since the ECHELON system was extended to cover New Zealand in the late 1980s,
the GCSB's Waihopai and Tangimoana stations -- and indeed all the British,
Canadian and Australian stations too -- can be seen as elements of a United
States system and as serving that system. The GCSB stations provide some
information for New Zealand government agencies, but the primary logic of these
stations is as parts of the global network.
On 2 December 1987, when Prime Minister David Lange announced plans to build the
Waihopai station, he issued a press statement explaining that the station would
provide greater independence in intelligence matters: "For years there has been
concern about our dependence on others for intelligence -- being hooked up to
the network of others and all that implies. This government is committed to
standing on its own two feet."
Lange believed the statement. Even as Prime Minister, no one had told him about
the ECHELON Dictionary system and the way that the Waihopai station would fit
into it. The government was not being told the truth by officials about New
Zealand's most important intelligence facility and was not being told at all
about ECHELON, New Zealand's most important tie into the United States
intelligence system. The Waihopai station could hardly have been more "hooked up
to the network of others", and to all that is implied by that connection.
Chapter 3 The power of the Dictionary: inside ECHELON Chapter 4 Fighting the
Cold War: the rold of UKUSA Chapter 5 The GCSB, ANZUS and a nuclear-free New
Zealand Chapter 6 Behind closed doors: what happens inside the GCSB Chapter 7
The organisation: secret structures of the GCSB Chapter 8 Secret squirrels: who
runs the GCSB Chapter 9 Station NZC-332: electronic eavesdropping from
Tangimoana Chapter 10 Under the radome: what happens at Waihopai Chapter 11 The
facts in the filofax: military signals intelligence missions Chapter 12 What are
the secrets? The intelligence product Chapter 13 Who watches the watchers?
Overseeing the intelligence agencies Chapter 14 Leaving the intelligence
alliance
1. The generally accepted definition of communications intelligence is
"technical and intelligence information derived from foreign communications by
someone other than the intended recipient. It does not include foreign press,
propaganda or public broadcasts." It generally refers to external intelligence
and so does not usually include governments spying on their own people.
2. Duncan Campbell, The Unsinkable Aircraft Carrier, Michael Joseph Ltd, London,
1984, p.167.
3. Rick Anderson, Seattle Times, 19 September 1982, p.1.
4. M. Long, World Satellite Almanac, second edition, Howard W. Sams & Company,
Indianapolis, 1987, pp. 206-208, 457-460.
5. James Bamford, The Puzzle Palace, Sidgwick & Guildford, London, 1983,
pp.167-171.
6. The station may not have been initially targeted on Intelsat. Some photos of
the station taken by Des Ball in June 1983 show the two interception dishes
facing directly skywards, meaning either that they were temporarily not being
used or that they were targeted at that time on satellites above East Asia (in
the early 1980s there were no Intelsats there).
7. A US$29 million project codenamed LADYLOVE at the station, for completion in
mid-1982, involved an "interim deployment" construction of one dish and a "new
operational electronic system" housed initially in equipment vans. A US$21
million "major new collection and processing complex with associated antenna
systems" followed in 1987.
8. Ascension Island is a 20-square kilometre British territory, situated halfway
between Brazil and Angola in the middle of the South Atlantic. It has a major
radio interception station with joint GCHQ/NSA staffing, a base for US
anti-submarine Orion aircraft, six separate radar and optical tracking stations
for US strategic missile tests and its large US-built airfield was the main
support base for the Falklands War (Richelson and Ball, The Ties that Bind,
Allen & Unwin, Boston, 1985, pp. 194, 201 and 220; Duncan Campbell, New
Statesman, "Report reveals island base, 21 May 1985).
9. Mary Louise O'Callaghan, Melbourne Age, "PNG to investigate Australian spy
claim", 26 November 1991, p.1.
10. For a full description of these "overhead" systems, see Jeffrey T.
Richelson, The US Intelligence Community, Ballinger, Cambridge, 1989.
11. Information from Jeffrey Richelson.
12. Mike Frost and Michel Gratton, Spyworld, 1994, Doubleday, Toronto. The book
describes in detail how and where these operations occurred.
13. Mike Frost helped to arrange a series of these operations, including
investigating the microwave routes through some cities while assessing the
suitability of the local Canadian embassy.
14. Brian Toohey and Marion Wilkinson, The Book of Leaks, Angus & Robertson,
Sydney, 1987, p.139.
15. Archie Hamilton, Minister of State for the Armed Forces, Written Answers to
Questions, British Parliament record for 9 June 1992, p.97.
16. Duncan Campbell, op. cit., p.168.
17. James Bamford, op. cit., p.102. Internal Menwith Hill station papers from
the early 1990s still referred to a computer-based communications system called
Platform.
18. Duncan Campbell, New Statesman, "They've got it taped', 12 August 1988,
pp.10-12.
MUST READ:
http://tangibleinfo.blogspot.com/2008/05/learned-helplessness-cia-mind-control.htmlfurther reading:
Ignorance Is Futile!








![]()